Software Research Center
At 0th Root, We are commited to building reliable and secure software for the connected world. We innovate, and develop new ideas, to solve problems in the space of inter-connected networks.
About Us
Started in 2010, as an independent research initiative, 0th Root was setup with a simple website to distribute software and provide documentation for users. Initially, our research involved understanding the SSH protocol and developing a library which can manage multiple servers remotely.
0th Root Software Research Private Limited was incorporated in April of 2013 to continue the research as an organization. It is headquarted in Bengaluru, India, and run efficiently by a team of committed professionals.
Our Mission
To research and build new technologies, to provide cost effective, reliable and secure software products to consumers, small, and medium enterprises without any hidden or overhead costs.
- New technologies
- Reliable and secure
- At affordable cost
Our Vision
To research and create new technologies in the field of computer software to help shift the Indian economy towards a product oriented growth.
- Product focused
- Research oriented
- Economic impact
Our Products
Cyber security protection for organizations, Networking utilities for web based remote access, and Developer tools to improve productivity in terminals
0th Root Secure Network
0SNet is a cyber security software that secures organization's internal web applications. It includes a certificate manager, user manager and a role-based access controls system.
0th Root Web Linker SSH
A Web based SSH client which provides a full fledged terminal on the web browser to manage remote hosts seemlessly.
0th Root See
A simple command line utility to run any command inside a virtual terminal to protect it from terminal hangups. This can be very useful when working remotely.

0th Root Secure Network
The quickest way to secure an organization's internal websites, without any impact to productivity, is by deploying 0SNet within the organization. It is a central place to manage access to all the internal websites via the in-built role-based access controls system.
Co-Founder, Exotel.
“A straight forward, easy to use solution that doesn't get in your way.”

0th Root Web Linker SSH
A secure HTTP/TLS server which provides a terminal on the web browser to allow login to remote hosts over SSH. The server accepts input over HTTP/TLS and translates them to standard terminal input for Secure Shell (SSH) Protocol. It is fully functional, mobile friendly, and supports all the features of a typical virtual terminal, including window resizing, copy-paste and scroll history.
Interested in integrating the solution into your platform ? Reach out to us.

0th Root See (0see)
Similar to terminal multiplexers such as screen and tmux, 0see implements a terminal emulator. However, 0see is not a multiplexer and it is primarily intended to protect commands run on the terminal from hangups.
Consider this as a modern replacement for nohup.
Blog Posts
RHEL/CentOS 7 Fix for Let's Encrypt Change
For TLS certificates issued by Let's Encrypt, the root certificate (DST Root CA X3) in the default chain expires on September 30, 2021. Due to their unique approach, the expired certificate will continue to be part of the certificate chain till 2024.…
TLS Explained — Issuer Authorization, Certificate Transparency, DANE, CAA
In TLS — Transport Layer Security, the client establishes a connection with the server and negotiates a TLS session to ensure confidentiality of the communication. However, this confidentiality is not guaranteed if the server is not verified.…
Let's Encrypt Change Affects OpenSSL 1.0.x and CentOS 7
Programs running on RHEL/CentOS 7 that use OpenSSL will fail to verify the certificate chain, or establish TLS connection, if the root certificate in the certificate root store is expired.…
Added Security Measures and Changes in TLS 1.3
A fine balance of usability, compatibility and security is maintained in TLS protocol. And, as technology matures, additional security guarantees are provided, such as forward secrecy, and older cryptographic algorithms are deprecated or their weaknesses are addressed.…
Exploring Application Layer Protocol Negotiation (ALPN)
The Internet protocol suite which forms the basis for modern Internet allows for different services to be provided by a single host. These services are assigned a port number and any connection to the port is assumed to be for that service.…
Negotiation of TLS Parameters for HTTPS Encryption
Browsing the web was originally insecure. However, with the use of Transport Layer Security (TLS) underneath, all of web traffic is nowadays encrypted. But before the data becomes encrypted, client and server negotiate encryption parameters in the form of Hello messages.…
How to Implement Zero Trust with TLS Client Certificates
As the word implies, in a zero-trust security model, no device or user is trusted. And, every request received by the system goes through the validation and authentication steps. This essentially means, no device or user enters the private network of the organization…
A Guide to Secure Internal Websites in 15 Minutes
It is common to not think about the security of the data stored and processed in your software system, until a disaster strikes. This can lead to significant difficulties later on, due to business interruptions, loss of customer trust, legal ramifications and challenges in securing the data.
Technology Stacks of Web Applications, 2020
Developing a web application requires multiple decisions to be made at an early stage. One of those decisions is the technology stack. While, in many cases, it would boil down to a personal choice, the typical factors include developers experience, production cost and project time frame.
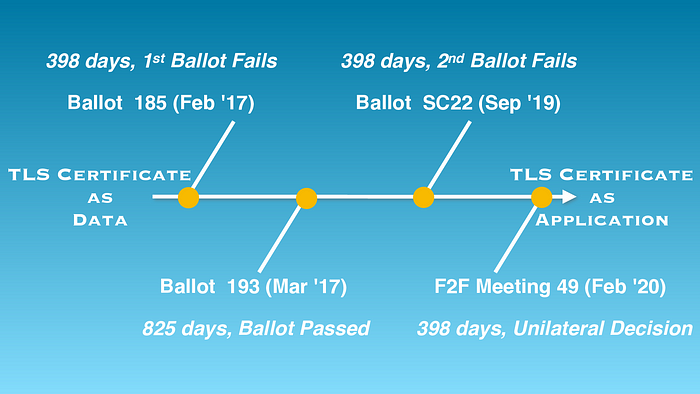
Lifetime of TLS certificate is now 398 days
Anyone who has ever browsed the internet should be aware of the small padlock icon on their browser's address bar. It is an indication that the content is loaded securely, and any information provided on the web page will be securely transmitted to website's servers. There are two parts to this padlock though,
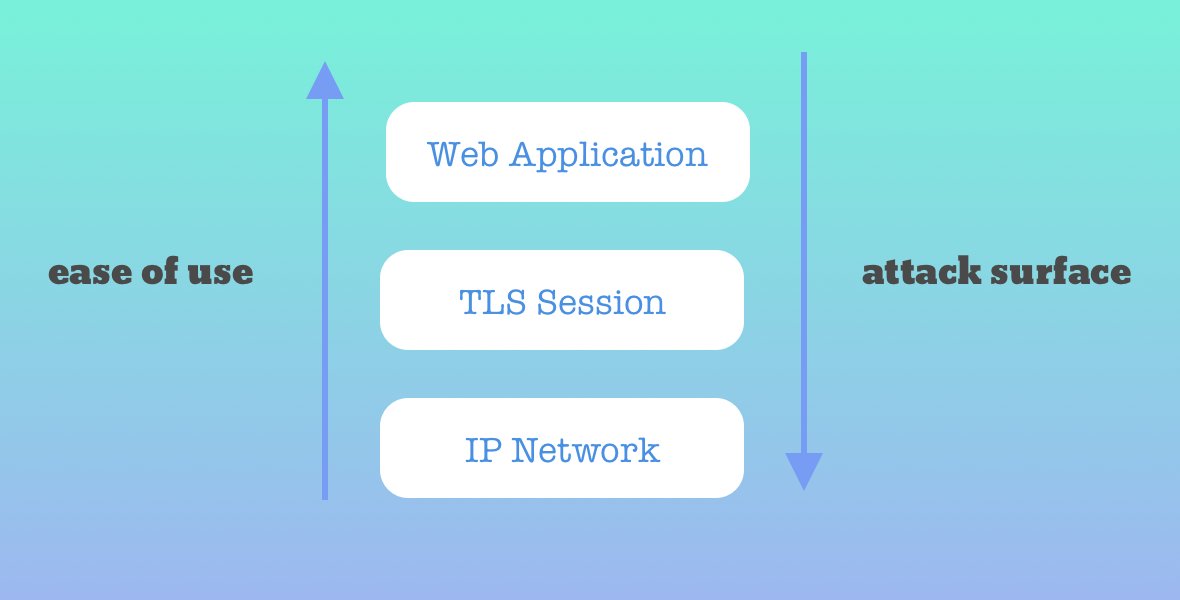
User authentication and Server protection
It is common to misunderstand adding user authentication as a way for securing the servers. While a layer of authentication can protect the web application from unauthorized users, the technology stack itself may not be protected.
Contact Us
RMZ Latitude Commercial,
10th Floor,
Bellary Rd, Hebbal,
Bengaluru - 560 024. (INDIA)
No.24, Tatia Nagar Phase -3,
Nolambur, Maduravoyal PO,
Chennai - 600 095. (INDIA)
+91 44 2653 2984
Copyright ©, 0th Root Software Research Private Limited. All rights reserved.